A mailing list I participate in has attracted a troll, which is a person who, deliberately or not, annoys everyone around him with ill-tempered, rude, and stupid questions. Our list's troll has managed to get himself suspended from Wikipedia about 10 times (he's still suspended), mostly for "incivil tone" and for missing the purpose of Wikipedia.
This kind of user has haunted every online community since The WELL and CompuServe—yea, even unto the days of the of dial-up BBS. This guy is simply the first troll we've seen on this particular list, though.
Even if Parker hadn't gotten fired two weeks ago, it looks like the building would have stopped him coming in anyway. We got this email earlier today, forwarded by the landlord:
We received a complaint about one of your tenants having a dog in the building. This was discovered by persons on the 5th floor hearing barking on the 4th floor. Hopefully I'm not confusing your unit with another but per the building rules and regulations policy that's attached to the Easement and Operating Agreement, only seeing eye dogs are permitted in the building.
Some people just don't like dogs. Their lives must be so sad.
I had meant to make a note of my 3,000th blog posting, but I completely forgot it was coming. So, after 2,353 days (and 24 minutes), three house moves, a few significant personal events, and Parker's entire life, The Daily Parker is still going strong.
At the historical posting rate for the blog (1.28 per day), I'll hit 6,000 entries in September 2018 and 10,000 entries by April 2027. (For the last two years, though, I've posted about 1.5 per day, so you could see 10,000 as early as April 2025.) Stick around.
And thanks for reading.
The FBI has put together a committee of university presidents to root out foreign spies who have infiltrated American colleges:
While overshadowed by espionage against corporations, efforts by foreign countries to penetrate universities have increased in the past five years, [Frank] Figliuzzi, [Federal Bureau of Investigation assistant director for counterintelligence] said. The FBI and academia, which have often been at loggerheads, are working together to combat the threat, he said.
Attempts by countries in East Asia, including China, to obtain classified or proprietary information by “academic solicitation,” such as requests to review academic papers or study with professors, jumped eightfold in 2010 from a year earlier, according to a 2011 U.S. Defense Department report. Such approaches from the Middle East doubled, it said.
The problem with this, as a number of people pointed out in the article, is that academics share information freely. That's their freaking job. And the U.S. has hundreds of thousands of foreign students—76,000 from China alone—because, for now anyway, we have the best schools in the world.
Of course the FBI should go after real spies, and discovering former Russian intelligence agent Sergei Tretyakov probably prevented Russia from stealing information that would have helped them catch up to where we'd gotten ten years earlier.
The university presidents on the FBI's committee need to remember their first duty. I hope some of them will remind the FBI that suspecting lots of foreigners of trying to spy on us will cost more than it will save.
This is a very old conversation. There are always people who see enemies everywhere. Sometimes they're right; but we need to make sure that when they're wrong, they don't cause more damage than they're trying to prevent.
I like being busy, but it does take time away from lower-priority pursuits like blogging. If I had more time, I'd pontificate on the following:
For now, though, it's back to the mines.
Some items that have gotten my attention:
More, I'm sure, later.
I found out, after too many failed download attempts for no reason I could ascertain (come on, Amazon), the 1940 Census data is also available on Ancestry.com. Their servers actually served the data correctly. And so, I found this:
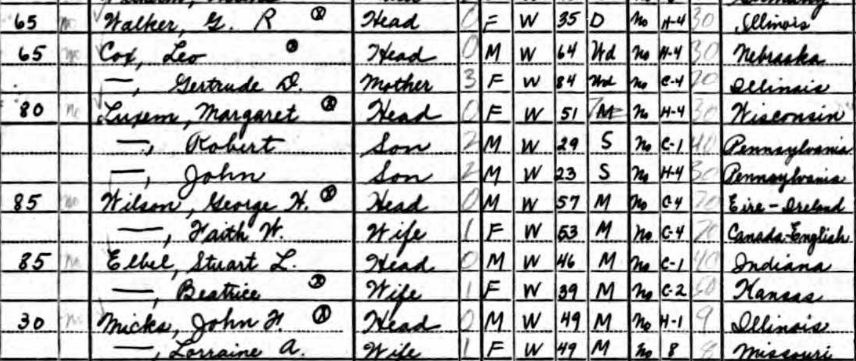
The apartment numbers aren't listed, and the building added an apartment to my entrance sometime in the last 70 years, but I think I can work it out. The first column shows the rent for each apartment. The three higher-rent apartments have to be the larger ones to the west. That means mine is either one of the two $65 apartments on the table or was vacant on 1 April 1940.
So the best I can do is that the three apartments on my side of the stairs that existed in 1940 contained a 35-year-old divorcée from Illinois who worked as an office manager in a brokerage, and a 64-year-old broker/solicitor from Nebraska who lived with his 84-year-old mother. My neighbors included a 51-year-old mother who lived with her 29- and 23-year-old sons, both of whom worked as wholesale salesmen; the 57-year-old treasurer of a wholesale varnish company and his 53-year-old wife; the 46-year-old head of the complaints department at Illinois Bell and his 39-year-old wife; and the building engineer and his wife, both of whom were 49.
All of these people were white, professional, and at least high-school educated. Six of eleven had college educations, a significantly higher proportion than the general public at the time. There were no children in the tier. All but two were U.S.-born. (The varnish-company treasurer came from the Republic of Ireland; his wife was English-Canadian.) All but the divorcée had lived in the same apartment for at least 5 years. Seven of eleven worked at least 40 hours during the previous week, including the poor janitor who worked 70. Salaries ranged from $600 (the 29-year-old son who sold furniture wholesale) to $5000+ (the Irish varnish company treasurer). Mrs. G.R. Walker, the most likely candidate for my predecessor in this apartment, made $2000, somewhat higher than the U.S. average salary in 1940 and approximately eqivalent to $32,000 today.
Today we're entirely professional (including three attorneys and two professional musicians), with a handful of young children, all of us college-educated or better. There is one foreign-born person; our average age, not counting the children, is about 38; and none of us worked 70 hours last week. Two of the seven apartments are rentals, the rest are owned. Adjusting for inflation, they cost almost exactly the same as in 1940.
In other words, the people who lived in my apartment building 70 years ago looked a lot like the people who live here today. And I wish I could meet them.
The Census and the National Archives have released the entire 1940 enumeration quasi-digitally. I think the data drop is great. I am going to download a few specific documents based on what I know about my own family, and about some of the places I've lived that were around in April 1940.
But as a software developer who works mainly with Cloud-based, large-data apps, I am puzzled by some of the National Archives' choices.
I say "quasi-digitally" because the National Archives didn't enter all the tabulated data per se; instead they scanned all the documents and put them out as massive JPEG images. I'm now downloading the data for one census tract, and the 29 MB ZIP file is taking forever to finish. The actual data I'm looking would take maybe 1-2 kB. That said, I understand it's a massive undertaking. There are hundreds of thousands of pages; obviously entering all the data would cost too much.
But this goes to the deeper problem: The Archives knew or should have known that they'd get millions of page views and thousands of download requests. So I need to ask, why did they make the following boneheaded technical decisions?
- They used classic ASP, an obsolete technology I haven't even used since 2001. The current Microsoft offering, ASP.NET MVC 3, is to classic ASP what a Boeing 787 is to a DC-3. It's an illuminated manuscript in the era of steam-driven presses.
- They organized the data by state and city, which makes sense, until you get to something the size of Chicago. Northfield Township, where I grew up, takes up one map and about 125 individual documents. Chicago has over 100 maps, which you have to navigate from map #1 to the end, and a ridiculous number of individual documents. You can search for the census tract you want by cross streets, but you can't search for the part of the city map you want by any visible means.
- I'm still waiting for my 32-page document after 22 minutes. Clearly the Archives don't have the bandwidth to handle this problem. Is this a budget issue? Perhaps Microsoft or Google could help here by donating some capacity until the rush is over?
In any event, once I get my documents, I'm going to spend some time going over them. I really want to find out what kind of people lived in my current apartment 70 years ago.
Update: The first download failed at 1.9 MB. The second attempt is at 6.6...and slowing down...
Update: The second and third attempts failed as well. I have, however, discovered that they've at least put the data out on Amazon Web Services. So...why are the downloads pooping out?
My company, 10th Magnitude, finally moved into its new office today. One of the criteria we had for selecting the new office was that they allow dogs. Everyone wins! (Hat tip MW.)

It's hard to tell who likes the Office Dog concept more, Parker or my co-workers:

Raganwald yesterday posted a facetious resignation outlining the dangers to employers of asking prospective employees to disclose social media information:
I have been interviewing senior hires for the crucial tech lead position on the Fizz Buzz team, and while several walked out in a huff when I asked them to let me look at their Facebook, one young lady smiled and said I could help myself. She logged into her Facebook as I requested, and as I followed the COO’s instructions to scan her timeline and friends list looking for evidence of moral turpitude, I became aware she was writing something on her iPad.
“Taking notes?” I asked politely.
“No,” she smiled, “Emailing a human rights lawyer I know.” To say that the tension in the room could be cut with a knife would be understatement of the highest order. “Oh?” I asked. I waited, and as I am an expert in out-waiting people, she eventually cracked and explained herself.
“If you are surfing my Facebook, you could reasonably be expected to discover that I am a Lesbian. Since discrimination against me on this basis is illegal in Ontario, I am just preparing myself for the possibility that you might refuse to hire me and instead hire someone who is a heterosexual but less qualified in any way. Likewise, if you do hire me, I might need to have your employment contracts disclosed to ensure you aren’t paying me less than any male and/or heterosexual colleagues with equivalent responsibilities and experience.”
Three things:
- He's right on the main point. Looking through employees' Facebook pages uninvited is tricky enough. Determining whether or not to hire someone based on a Facebook page is closer to the line. Forcing the disclosure crosses the line, surveys the land, plants a flag, and invites the natives to kill you in your sleep.
- Disclosing a password to anyone for any reason is, almost always, a bad idea. Authentication is half of security (the other is authorization, which depends on you being who you say you are). The corollary to authentication is deniability. If you lose control over your Facebook password, you expose yourself to identity theft. To emphasize this point, in our office we routinely prank developers who leave their keyboards unlocked when they leave the room. Walking away at a client site could let clients see other clients' materials, for starters, but it also could allow someone to send email or make Facebook posts in your name.
- I am proud to report that Illinois is right now passing a law to prohibit this practice. It will probably be signed later this month.